Computer-network security breaches are never out of the news for long, but lately, they’ve been hogging the headlines: the Sony hack, the Uber hack, and last month, the revelation that an international gang of cybercriminals had used malware to steal an estimated billion dollars from financial institutions over two years.
In this context, MIT yesterday announced plans to address the problem of cybersecurity from three angles: technology, public policy, and organizational management.
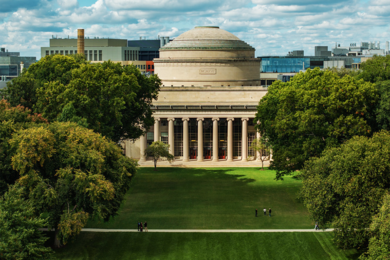
At an event at MIT’s Stata Center, the home of the Computer Science and Artificial Intelligence Laboratory (CSAIL), with more than 200 students, academics, and industry representatives in attendance, MIT faculty and administrators unveiled three new cybersecurity initiatives, to be housed at CSAIL and the MIT Sloan School of Management.
Funded with a $15 million grant from the Hewlett Foundation, the MIT Cybersecurity Policy Initiative will pool the expertise of researchers at CSAIL, MIT Sloan, the MIT departments of political science and economics, and the Science, Technology, and Society program to better characterize the security dynamics of large networked systems, with the aim of guiding policymakers.
Cybersecurity@CSAIL will provide funding and coordination for the lab’s ongoing research into hardware- and software-based approaches to computer security, while MIT Sloan’s Interdisciplinary Consortium for Improving Critical Infrastructure in Cybersecurity, or (IC)3, will focus on the human element — how organizations can ensure that their employees or volunteers are not creating security vulnerabilities, whether intentionally or not.
The launch event was emceed by Maria Zuber, MIT’s vice president for research, and the speakers included representatives of each of the three initiatives and MIT President L. Rafael Reif.
In his opening remarks, Reif emphasized both the new initiatives’ partnerships with industry and the interdependence of their research programs. “New technologies will require new policies and incentives,” he said. “Emerging policies must adapt to future technologies. And none of that matters if they cannot make the present a safe place to do business.”
“Security by default”
Reif was followed by Daniela Rus, the Viterbi Professor of Electrical Engineering and Computer Science and director of CSAIL. Rus began by emphasizing MIT’s long history of involvement in cybersecurity: as the home of one of the first computers to allow multiple simultaneous users, it was also the birthplace of the computer password.
But Rus also gave some sense of what the future of cybersecurity would look like. “Many of today’s cybersecurity issues stem from older, poorly designed systems that viewed security as an afterthought,” she said. “Organizations learned to ‘patch and pray,’ planning to manage attacks as they happened rather than fighting them systematically. But we can change that. Instead of looking for patches, we can move towards security by default.”
Rus then introduced Howard Shrobe, a principal research scientist at CSAIL, who will direct Cybersecurity@CSAIL. Shrobe elaborated on Rus’s historical observations, pointing out that the researchers who developed MIT’s multiuser computer, under the auspices of Project MAC, in fact wrote an operating system that had “security by default.” But the computers of the time simply weren’t powerful enough to execute its security protocols efficiently.
Today, however, “on every criterion that you can think of, machines are 50,000 times more powerful than when Project MAC started,” Shrobe said. “We can now start to use those resources to enforce security in a systematic way.”
Cybersecurity@CSAIL, Shrobe added, would focus on three themes: prevention, or designing systems that are harder to hack; resilience, or designing systems that can offer secure transactions even after they’ve been compromised; and regeneration, or designing systems that can repair themselves when breaches are detected.
The founding member companies of Cybersecurity@CSAIL are BAE Systems, BBVA, Boeing, BP and Raytheon.
Square one
Danny Weitzner, a CSAIL principal research scientist and director of the new Cybersecurity Policy Initiative, took the podium next. No one, Weitzner said — neither researchers nor policy makers — has a very good understanding of the dynamics of cybersecurity. But that doesn’t prevent policy makers from trying to control them.
“The United States government, in last year’s budget, is spending over $13 billion on cybersecurity efforts,” Weitzner said. “That’s 1 percent of discretionary spending.”
Weitzner then offered an example from his own two-year stint as the U.S. deputy chief technology officer for Internet policy. During that time, he said, the U.S. Congress was debating the Stop Online Piracy Act, which included what Weitzner called a “seemingly simple proposal to require Internet service providers to use some features of the domain name system to block access to [content pirates’] websites.”
Discussions of the proposal elicited a letter from 83 distinguished Internet engineers — including MIT’s David Clark, who was the Internet’s chief architect for most of the 1980s — who argued that tampering with the Internet’s domain name system, which translates human-readable URLs into machine-readable IP addresses, could have potentially disastrous consequences.
“Their intuition as really good Internet engineers was that it could cause some problems,” Weitzner said. “But really, there was no science presented, no formal model of the interaction between the domain name system and the rest of the Internet — certainly no understanding of how individuals would behave at large scales.” Generating that type of multidisciplinary model is one of the goals of the Cybersecurity Policy Initiative.
Human factors
S. P. Kothari, the Gordon Y. Billard Professor in Management and deputy dean at MIT Sloan, then introduced the final speaker, Stuart Madnick, the Maguire Professor of Information Technologies at MIT Sloan and a professor of engineering systems, who will lead (IC)3.
“It’s great to hear about the work being done to improve the technology by our colleagues at CSAIL and the regulatory considerations being studied by CPI,” Madnick said. “But various studies have shown that up to 80 percent of the incidents [of cybersecurity breaches] are aided or abetted by authorized users.”
“Understanding the organizational, managerial, and strategic issues about cybersecurity is of great importance to protecting our critical infrastructure,” he added, “and that is the focus of (IC)3.”