Lincoln Laboratory recently unveiled LLCipher, a new outreach program for high school students. LLCipher is a one-week cryptography workshop that provides an introduction to modern cryptography — a math-based, theoretical approach to securing data.
Lessons in abstract algebra, number theory, and complexity theory provide students with the foundational knowledge needed to understand theoretical cryptography. Students build on that knowledge to construct provably secure encryption and digital signature schemes. On the last day, the students learn about some less mainstream developments in cryptography. Guest speakers cover various techniques that enable multiple entities to exchange data without disclosing to one another more data than necessary to perform a particular function. These include zero-knowledge proofs (proving a statement is true without revealing any information beyond the truth of the statement) and multiparty computation (computing a function over multiple parties’ inputs while keeping the inputs private)."
The course, held at Lincoln Laboratory's Beaver Works facility near MIT campus, came about with the help of Bradley Orchard of the laboratory's Advanced Sensor Systems and Test Beds Group and Sophia Yakoubov, Emily Shen, and David Wilson, all of the Secure Resilient Systems and Technology Group.
Orchard conceived the idea for LLCipher while teaching high-school students at the Russian School of Mathematics in Lexington, Massachusetts. He noticed a significant need for additional learning opportunities beyond what is offered in even the best high schools. Orchard noticed some very bright students were ready for material beyond calculus. "I thought it would be fun to offer a short introductory summer course for advanced high-school students," he said. "I naturally thought of cryptography because it combines beautiful mathematics with powerful, useful, and fun techniques, and most importantly, aspects of cryptography are very accessible to advanced students."
To design the course, Orchard asked for help from the laboratory's management; John Wilkinson, leader of the Cyber Systems Assessments Group; and cryptography experts including Yakoubov, who, knowing how much she enjoyed teaching the CyberPatriot students, was eager to get involved.
"I cannot emphasize how difficult it is to design a short course that is effective, interesting, and fun for high-school students," Orchard said. "Sophia did a superb job accomplishing this task, as evidenced by the enthusiasm and participation of the students. The students were engaged, asking questions, and demonstrating that they understood the material, and, most importantly, having fun."
Chiamaka Agbasi-Porter of the Communications and Community Outreach Office handled the student applications and class logistics. Agbasi-Porter indicated that each of the 16 selected students were able to express their enjoyment of math through independent projects in their application to be a part of LLCipher. She felt the students for this pilot class were smart and enthusiastic. Yakoubov agreed: "The class was very interactive and the students were engaged in the topic; their questions and ideas made them a pleasure to teach."
The first thing covered in class was encryption. The instructors started by explaining the one-time pad, which is a perfectly secure encryption scheme, meaning that an eavesdropping adversary cannot learn anything about the encrypted message no matter how much computing power he or she has. Perfectly secure encryption schemes have a significant drawback, however: The secret key shared by the message sender (typically called "Alice" in the industry) and message receiver (referred to as "Bob") has to be at least as long as the message itself. Alice might want to send Bob very long messages, and might not know in advance how long these messages will be, so establishing a sufficiently long key might be problematic.
The class discussed computationally secure encryption schemes, which allow Alice and Bob to use smaller keys, but assume that the eavesdropping adversary has a bounded amount of computing resources available. This does not cause problems in practice if the correct parameters are used. This bound can be made so large that all of the computing power on earth doesn't come close to exceeding it. Building on a foundation of modular arithmetic and number theory, the students learned how to construct two computationally secure encryption schemes: stream ciphers, which rely on a shared secret, and the El Gamal encryption scheme, which does not rely on a shared secret. (It is a public key encryption scheme.)
The instructor also spoke about digital signatures, which ensure the integrity of the message — i.e., they allow Bob to check that the message being delivered is the same one which was sent by Alice, and that it wasn't tampered with by an adversary en route.
On the last day of class, two guest speakers covered newer and less mainstream topics in cryptography. David Wilson taught zero knowledge proofs, which are techniques that allow Alice to prove any statement to Bob without having to reveal anything at all beyond the statement itself. This is very counterintuitive; Alice can prove a statement like "I know the factors large number n" without sharing the factors themselves.
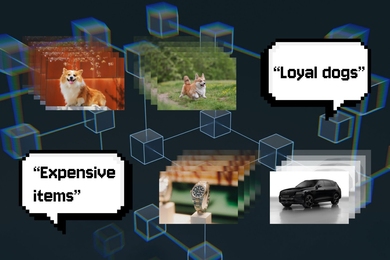
Emily Shen taught multiparty computation, a tool that allows multiple entities with secret inputs to compute a joint function on their inputs without having to reveal anything beyond the output of the joint function. For instance, using multiparty computation, people can figure out their average salary without anyone having to reveal their individual salary.
When asked about the most interesting thing he learned, one student replied, "Zero-knowledge proofs, as they seemed impossible. The idea of proving knowledge without sharing it is fascinating." Another student captured the essence of the course by saying, "My favorite thing about the class was learning about cryptography, as it was different from traditional math and required a different type of thinking."
Yakoubov maintains that the first LLCipher workshop was clearly a success. "We definitely plan to offer it again next year," she said. "The most common suggestion for improvement was making the program longer, which we plan to do by adding activities."
"My hope is that this is the beginning of a series of short courses that introduce these bright high-school kids to cryptography and, in general, mathematics," Orchard said. "There is such a need out there, both for the students and the cyber community." Agbasi-Porter added, "The students practiced critical thinking while learning about cybersecurity — an industry which will clearly be growing in the future. That's a definite advantage for the students of this course."