Security breaches make the news with depressing regularity. Retailers including Target, Home Depot, and Staples have been hacked, giving cybercriminals access to customers’ credit-card numbers or other personal information, from email addresses to phone numbers.
So-called "spear-phishing" attacks, such as payroll scams at universities, have taken phishing to a new level. Criminal hackers collect information about a given community and then send targeted emails to try to harvest passwords or other credentials.
On top of this, substantial increases in computing power have made it easier than ever to break passwords. Beyond ditching your devices and hiding in a cave, what can you do to protect sensitive data?
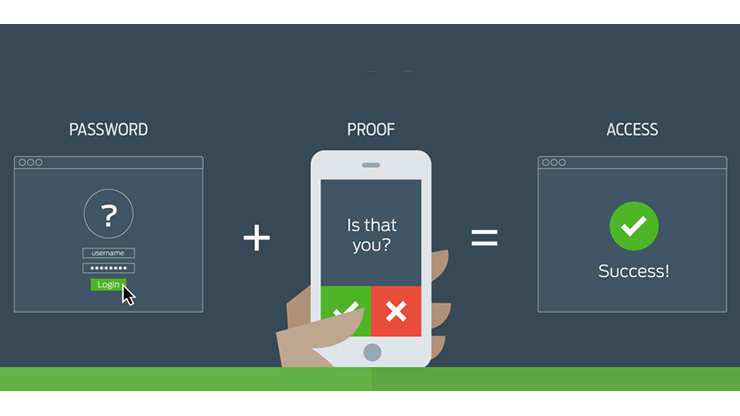
Benefits of two-factor authentication
One way to strengthen security is to use two-factor authentication (2FA). Twitter, Google, Facebook, Dropbox, Apple, and Microsoft all offer it, as does Blizzard Entertainment in its "World of Warcraft" game. As Information Systems and Technology (IS&T) manager Garry Zacheiss notes, “If people are using two-factor authentication to protect their fake money in a video game, shouldn’t we be using it to protect our real assets at MIT?”
The answer is yes. IS&T is now providing access to Duo, a two-factor authentication system from Duo Security. It’s being used for Touchstone-enabled Web applications at MIT – from Atlas and Stellar to the Roles Database and MIT Wiki Service.
But let’s backtrack a moment: Just what is a factor? In cyberspeak, a factor is something the user "knows" (such as a password), "is" (such as a fingerprint), or "has" (such as a smartphone). Adding a second authentication factor to a login, beyond a password, makes the process much more secure. Even if hackers steal your password, they can’t pretend they’re you if they don’t have access to your smartphone or have your fingerprint (literally) on hand.
Duo at MIT
After in-house testing and a successful pilot, IS&T is making Duo available to the MIT community. This self-service Web application lets you:
- enroll with Duo Security if you’re a new user;
- associate a phone or phones with your Duo account;
- manage existing devices associated with your account; and
- enable Duo authentication as a requirement for Touchstone logins.
Zacheiss recommends that community members sign up for Duo with their smartphones, since they offer the best user experience, via Duo Push. If you don’t own a smartphone, you can opt to receive authenticating robocalls on your land line.
To learn more about installing and using Duo at MIT, visit the Two-Factor Authentication with Duo page in the IS&T Knowledge Base. You may also want to check out Duo’s Guide to Two-Factor Authentication. If you have questions, contact the IS&T Computing Help Desk at helpdesk@mit.edu or 617-253-1101.