Heartbleed Bug — take steps to protect your information
Learn how IS&T is dealing with the OpenSSL Heartbleed Bug and what you need to know about it, including steps to ensure your accounts and sensitive data are secure.
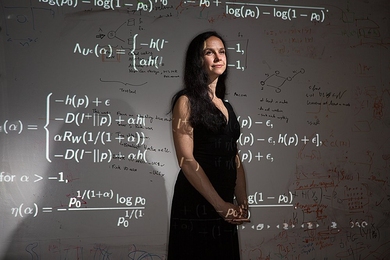
Modeling cyberspace control worldwide
Nazli Choucri analyzes issues of governance, politics, and participation in online communications.
Beware of email phishing
Phishing is a ploy to get you to click on bogus links or disclose your username and password, giving attackers a way to access your email account.
Encryption is less secure than we thought
For 65 years, most information-theoretic analyses of cryptographic systems have made a mathematical assumption that turns out to be wrong.
MIT strengthens network password requirements
Stronger Kerberos password rules and password expiration policies now tied to annual certificate renewal process
Protecting data in the cloud
A new hardware design makes data encryption more secure by disguising cloud servers’ memory-access patterns.
Securing the cloud
A new algorithm solves a major problem with homomorphic encryption, which would let Web servers process data without decrypting it.
Making quantum encryption practical
An MIT team that proposed a new, more-practical scheme for using quantum physics to secure data transmission has now demonstrated it experimentally.
What is email spoofing all about?
In this modern form of forgery, email information is masked in an attempt to trick recipients into believing the message came from someone else.
Daniel Weitzner receives IAPP Privacy Leadership Award
Lauded for work and leadership in the development of Internet public policy
Beefing up public-key encryption
MIT researchers show how to secure widely used encryption schemes against attackers who have intercepted examples of successful decryption.
IS&T recommends Firefox users upgrade to Firefox ESR 17
The Extended Support Release (ESR) of Firefox is designed for institutions like MIT.
IS&T addresses concerns about MIT’s network
Information Services & Technology sheds light on recent service interruptions, as well as steps taken to mitigate risks to the MIT network.
Securing your eW-2 tax form
As with any personal data accessed online, there are measures that can be taken to minimize risk.